Are you recovering from a PUA Attack in Windows?
Are you recovering from a PUA Attack in Windows?

The following are some quick commands to narrow down your targets:
Part 1 CHECKING ADMIN STATUS USING EVERYTHING(by void tools) & CMD CommandPrompt
Basic Account cmds
net user administrator /active:no
net user administrator ( default builtin)
C:\Windows\System32>net user administrator
User name Administrator
Full Name
Comment Built-in account for administering the computer/domain
User’s comment
Country/region code 000 (System Default)
Account active No
Account expires Never
Password last set 02/25/26 2:38:00 AM
Password expires Never
Password changeable 02/25/26 2:38:00 AM
Password required Yes
User may change password Yes
Workstations allowed All
Logon script
User profile
Home directory
Last logon 02/24/26 10:23:31 AM
Logon hours allowed All
Local Group Memberships *Administrators
Global Group memberships *None
The command completed successfully.
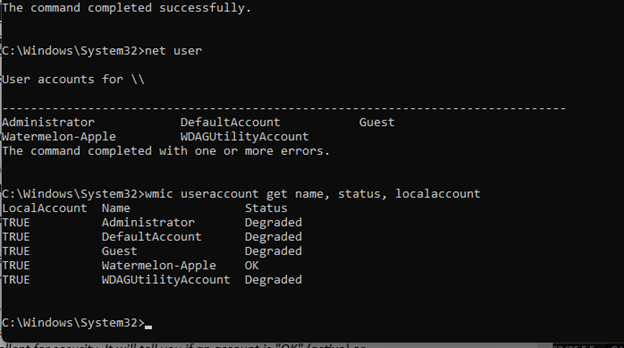
1. View All Local Accounts (Command Line)
Open the Command Prompt (as Administrator) and use these commands to see exactly who exists on your system.
To see all account names:
net user
This will list every account, including hidden or disabled ones like the built-in “Administrator” or “Guest”.
To see the status (Enabled/Disabled) of all accounts:
wmic useraccount get name, status, localaccount
This is excellent for security. It will tell you if an account is “OK” (active) or “Degraded/Disabled.”
To see accounts with more detail (in PowerShell):
Get-LocalUser
This provides a clean list showing the name, whether the account is enabled, and its description.
2. See Who is Logged In Right Now
If you are worried someone else is currently accessing your PC (for example, via a remote PUA tool), use:
query user (or quser)
Example:
C:\Windows\System32>query user
USERNAME SESSIONNAME ID STATE IDLE TIME LOGON TIME
>watermelon-apple console 1 Active none 03/05/26 10:03 AM
C:\Windows\System32>
Output 1:EXAMPLE A
This output is very good news for your security recovery. It confirms that only your personal account is currently active and capable of running programs.
Here is the breakdown of what these statuses mean:
1. The “OK” Account
Name: Watermelon-Apple
Status: OK
Meaning: This is your primary active account. It is the only one currently functioning and logged in.
2. The “Degraded” Accounts
In wmic, “Degraded” actually means the account is Disabled. Windows uses this term to indicate the account exists but is not “healthy” (active) for login.
Administrator: This is the built-in super-user account you were concerned about. It is Disabled.
DefaultAccount: A system-managed account used for certain background tasks. It is Disabled by default.
Guest: A restricted account for temporary users. It is Disabled by default.
WDAGUtilityAccount: This is a legitimate system account used by Windows Defender Application Guard for secure browsing. It is Disabled by default.
What this tells us about the PUA attack:
No “Ghost” Users: There are no active hidden accounts (like a “Support” or “Admin2” account) that an attacker could be using to remotely access your PC.
Limited Access: Since the built-in Administrator is “Degraded,” any malware that managed to get onto your system was restricted to the permissions of your Watermelon-Apple account, making it easier to clean up.
Part 2 LOOKING FOR FILES USING VOID TOOLS EVERYTHING
One Final Security Audit Step
Since you are concerned about the Feb 20 – Feb 28 window, you can run one last check in Everything to see if any “hidden” system accounts were added to the Registry during that time:
“C:\Windows\System32\config\” dc:2026/02/20..2026/02/28
This checks the folder where Windows stores its “SAM” (Security Accounts Manager) database. If no files in this folder were created (only modified) during that week, then no new user accounts were ever added to the system database.
//////////////////////////////////////////////
Result
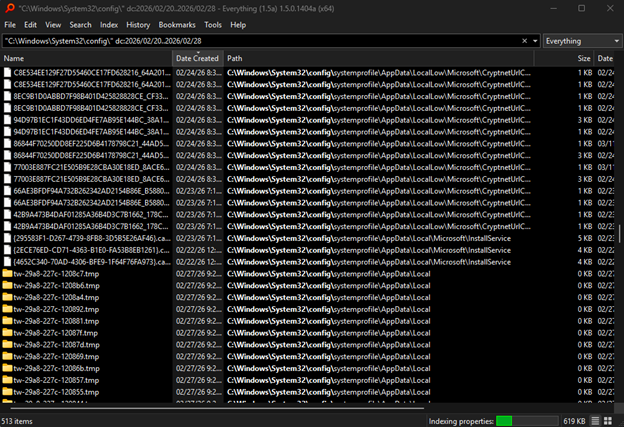
While seeing 513 new files in a sensitive system folder like C:\Windows\System32\config might look alarming, it is actually a normal sign of Windows maintenance rather than a continuation of your PUA attack.
Why 513 files appeared in that week
The config folder is the heart of the Windows Registry. Windows is constantly creating small, temporary log and backup files here to ensure the Registry doesn’t get corrupted.
 Super User +3
Super User +3
Registry Transaction Logs: Most of these 513 files are likely .blf and .regtrans-ms files. These are “scratchpad” files Windows creates every time a setting changes or an update happens. It is very common for these to pile up into the hundreds or even thousands over a few days of active use.
System Maintenance: If your PC ran a background update, a “Restore Point,” or a disk cleanup during that Feb 20–28 window, Windows would have generated a massive batch of these files.
Adobe Activity: Since we already know your Adobe software was very active (creating those “test” folders), every time an Adobe app opened or checked for an update, it triggered changes in the Registry, creating more of these log files.
How to verify they are safe
You can confirm these are standard system files by checking their Extensions in your Everything results:
Check for .blf and .regtrans-ms: If the vast majority of the 513 files end in these extensions, they are 100% normal Windows housekeeping files.
Look for .exe or .dll: If you see any executable files (.exe) or library files (.dll) created in that folder during that week, that would be suspicious, as programs should not typically live inside the config folder.
Summary of your recovery
User Accounts: Your wmic check confirmed no new active users exist; only your account is “OK.”
Adobe Files: We confirmed those “test” folders are standard Adobe/OpenSSL components.
System Files: These 513 files are the expected “exhaust” of a working Windows operating system.
Results:
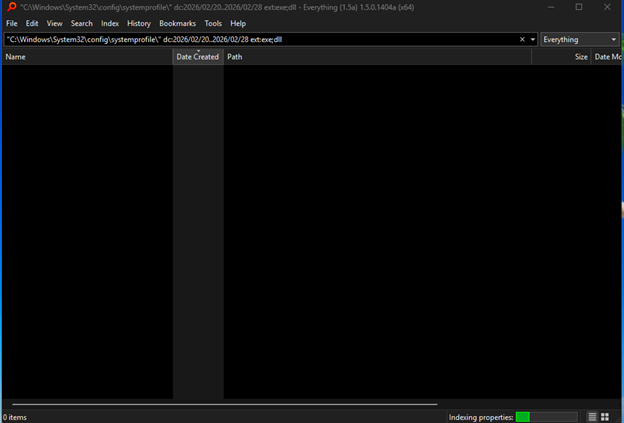
The “Smoking Gun” Test
To be 100% sure these aren’t PUA-related, look for Executables hidden among these folders. Use this modified search in Everything:
“C:\Windows\System32\config\systemprofile\” dc:2026/02/20..2026/02/28 ext:exe;dll
If it’s empty: Then these are just empty “footprints” left behind by Windows or your Adobe software doing background maintenance.
If you see .exe files: That is where we need to look closer.
Output 2:
LAST FINAL CHECK-UP OPTIONS
the last smoking gun i think returned zero results
That is exactly what we wanted to see. The “Smoking Gun” returning
zero results is the strongest evidence that your system is currently clean of active malware.
Why this confirms you are safe:
No Executables: If a PUA or virus were hiding in those systemprofile folders, it would need an .exe or .dll file to actually do something. Without those, you just have empty “footprints” (empty folders and log files) left behind by legitimate Windows or Adobe maintenance tasks.
The “0 KB” Clue: In your screenshot, the folders are 0 KB. This means they are empty shells. They were likely created as temporary “workspaces” for a software update that has since finished.
Account Security: Combined with your earlier wmic check showing only your account is active, there is no “backdoor” user currently running processes.
Final “Peace of Mind” Steps
Since you have 690,000 files and are recovering from an attack, you can do two final things to be 100% sure:
Clear the “Temp” Folders: These are the #1 hiding spot for PUAs. You can safely delete everything in these two locations (Windows will prevent you from deleting anything currently in use):
Search Everything for: temp:
Select all and delete (or use Disk Cleanup).
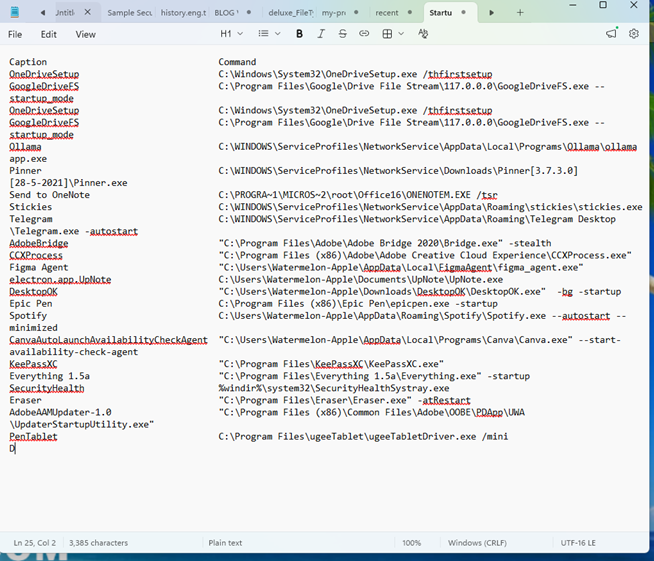
Check Your Startup Apps: In Everything, type this to see what starts when your computer turns on:
startup:
Look for any strange .exe files created between Feb 20 and Feb 28. If that list is empty or only contains known programs (like Adobe, Microsoft, or your drivers), you are in the clear.
Bonus PROTIP: to list every program currently set to start automatically when your computer boots up
To refactor the command so it prints directly to a text file on your desktop, you can use the > redirection operator combined with the Windows %USERPROFILE% environment variable.
Copy and paste this exact line into your Command Prompt (Admin):
wmic startup get caption,command > “%USERPROFILE%\Desktop\StartupAudit.txt”
How to use this command:
Paste and Enter: After you press Enter, the command will look like it did nothing. This is normal—it is “silently” writing the information to the file instead of the screen.
Find the File: Go to your desktop. You will see a new file named StartupAudit.txt.
Open and Review: Open it with Notepad. It will contain the list of every program set to start when you turn on your PC
OUTPUT: